References in Montreal Accord on Patient-Reported Outcomes (PROs) use series – Paper 9: anonymization and ethics considerations for capturing and sharing patient reported outcomes - Journal of Clinical Epidemiology

Primer on GDPR Pseudonymization. Personal data is any information… | by Balaji Ramakrishnan | Medium

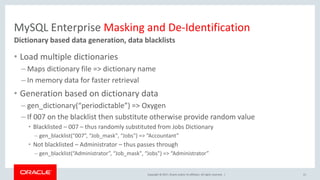
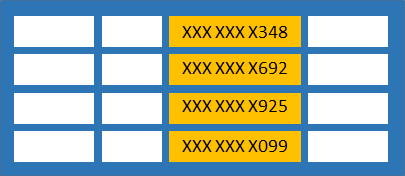
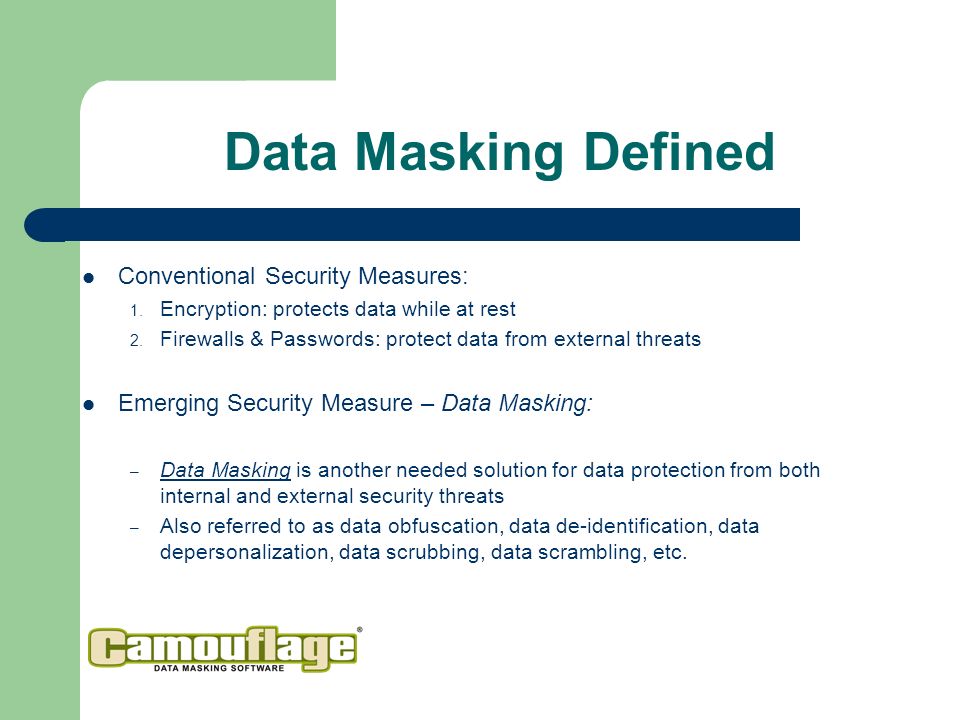
Informatica Persistent Data Masking VS Informatica Dynamic Data Masking - compare differences & reviews?

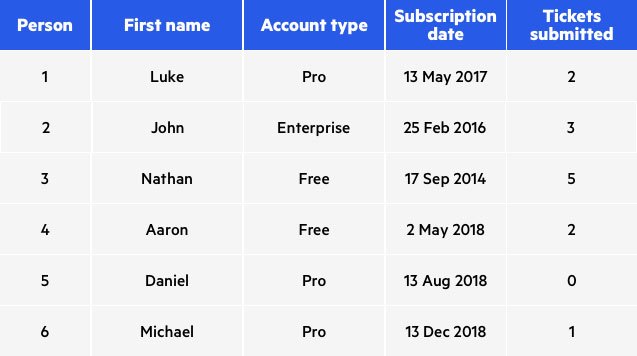
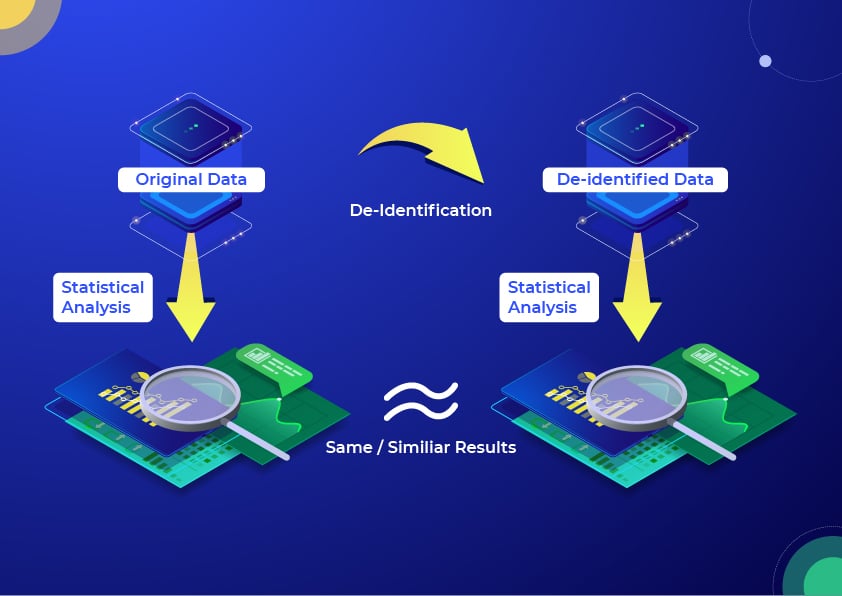
De-identification and re-identification of PII in large-scale datasets using Cloud DLP | Cloud Architecture Center | Google Cloud
![Data Masking and Encryption Are Different [video] - IRI Data Masking and Encryption Are Different [video] - IRI](https://i.ytimg.com/vi/LuO7bi9uRh4/maxresdefault.jpg)