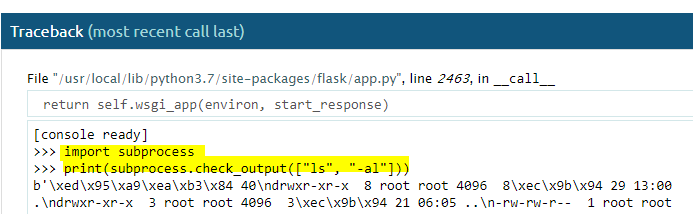
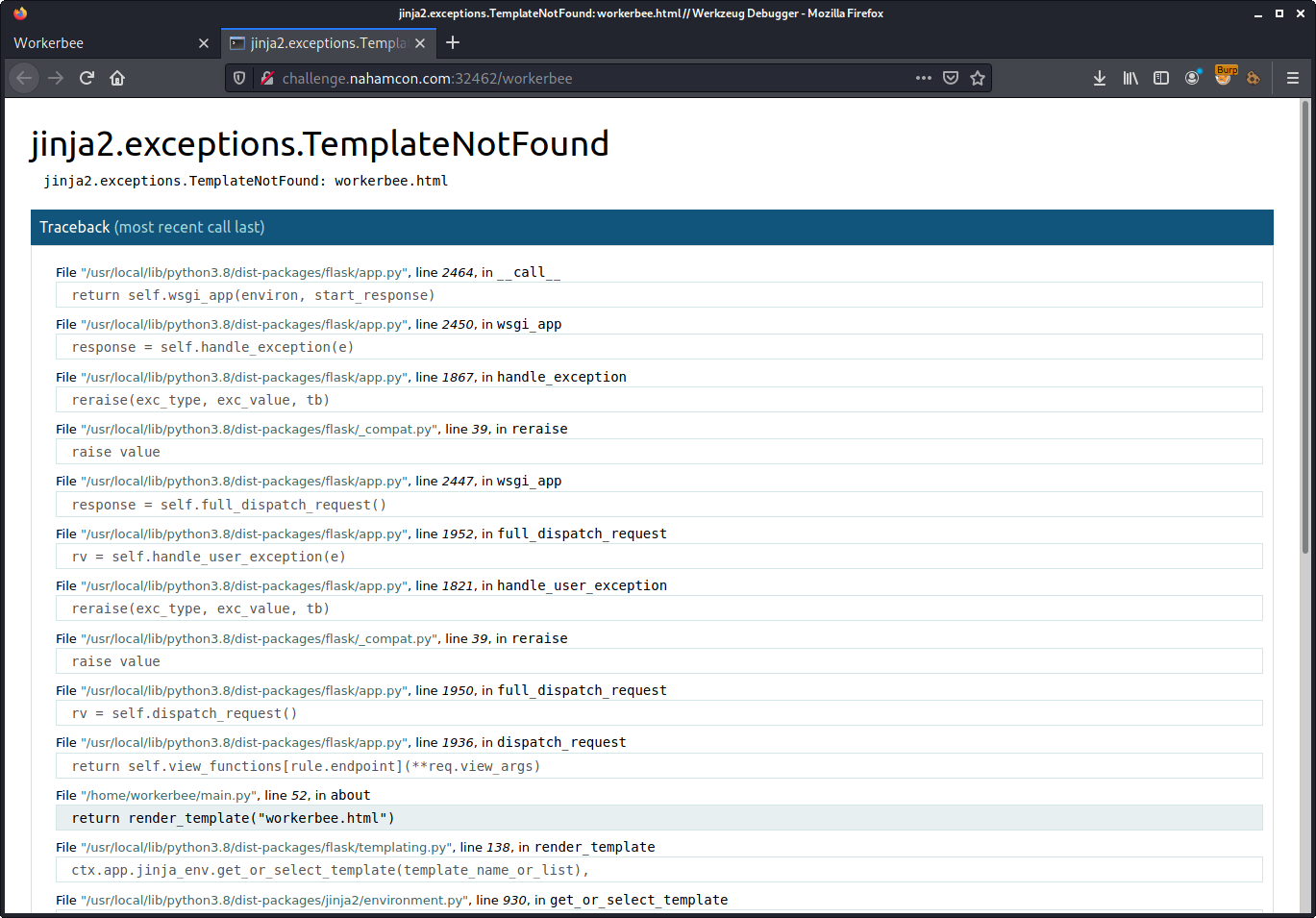
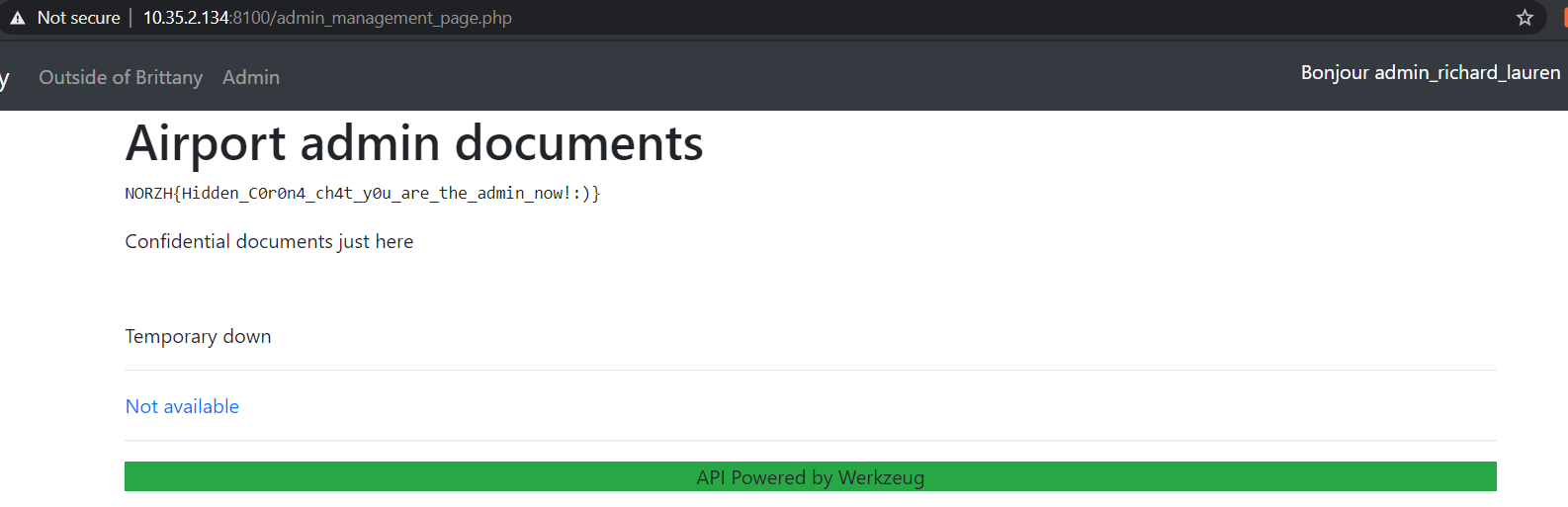
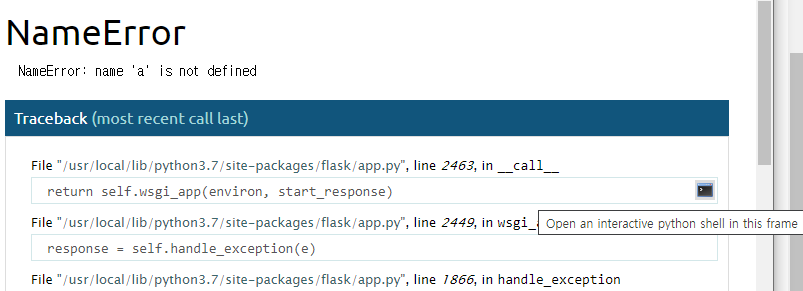
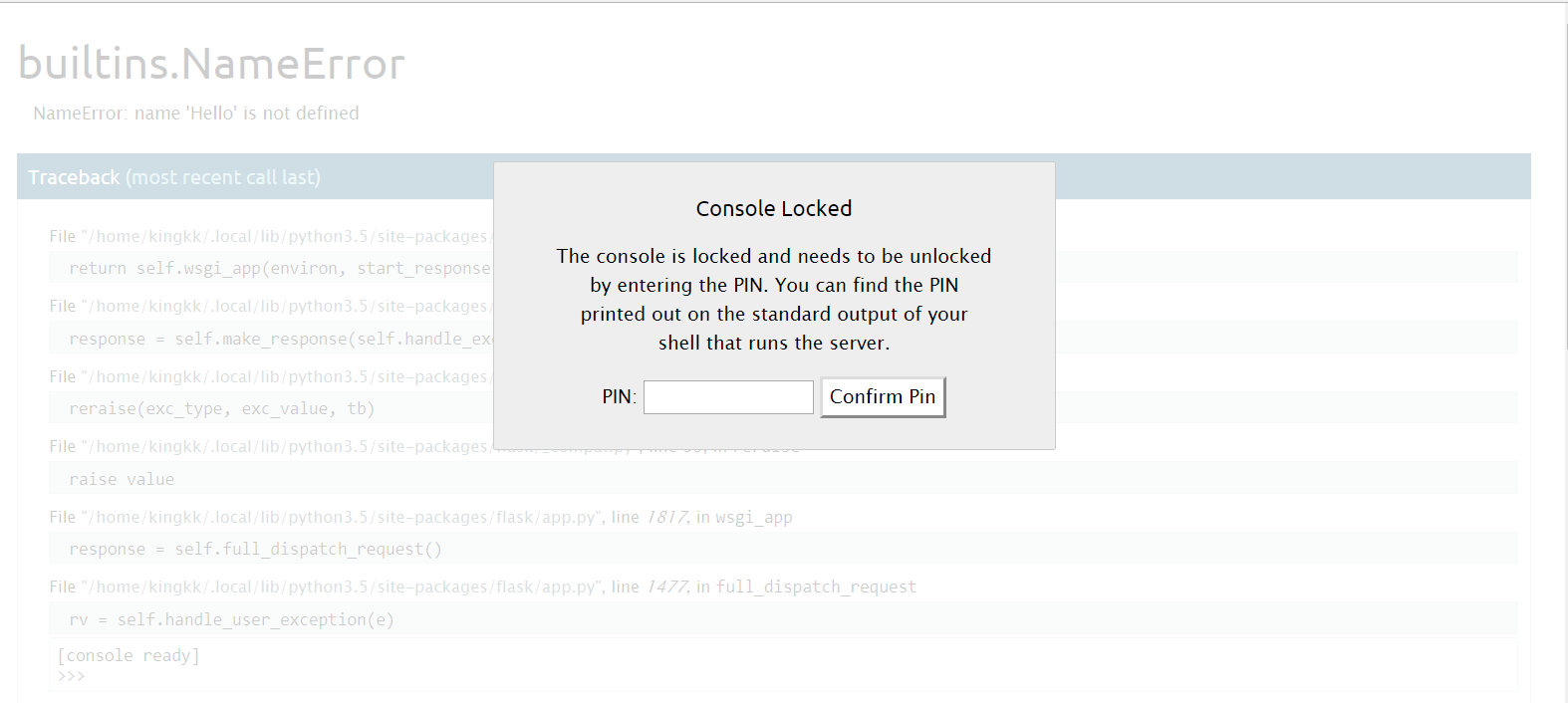
Hacking Flask Applications. Executing arbitrary commands using the… | by Vickie Li | The Startup | Medium
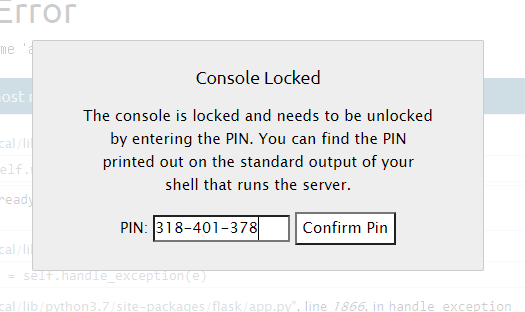
Werkzeug has a debug console that requires a pin. It's possible to bypass this with an LFI vulnerability or use it as a local privilege escalation vector. | PythonRepo
GitHub - wdahlenburg/werkzeug-debug-console-bypass: Werkzeug has a debug console that requires a pin. It's possible to bypass this with an LFI vulnerability or use it as a local privilege escalation vector.